Zero Trust Network Access for SMB
The Zero Trust foundation your business needs.

The Zero Trust foundation your business needs.


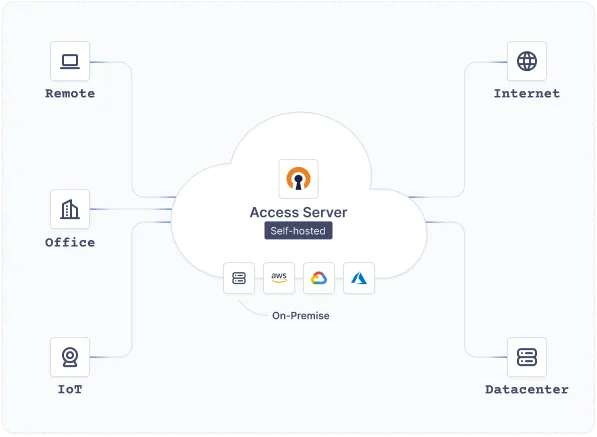
Never trust, always verify. With Access Server, you can protect workers using home and public WiFi networks, and SaaS applications, outside your network perimeter. Access Server provides all the tools and capabilities necessary for building a strong Zero Trust Network Access (ZTNA) architecture — one that blocks or significantly mitigates attacks before they reach your critical resources.
ZTNA goes beyond traditional VPN by continuously validating every user, device, and connection — not just at login, but throughout the entire session. Access Server makes it straightforward to deploy and manage a Zero Trust Network Access strategy that scales with your business, whether your workforce is in the office, remote, or anywhere in between.
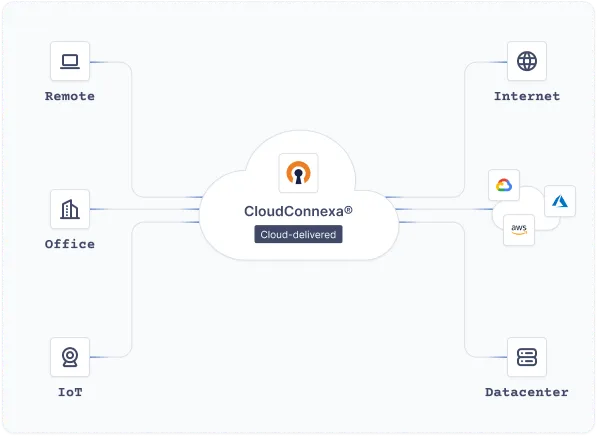
CloudConnexa provides all the tools and capabilities necessary to build a strong Zero Trust Network Access (ZTNA) architecture that blocks or significantly mitigates attacks. Businesses of all sizes can deploy a ZTNA strategy through a secure virtualized network that expands access controls and protects workers using home and public WiFi networks — well beyond the limits of your traditional network perimeter.
By embedding Zero Trust Network Access principles directly into your network fabric, CloudConnexa ensures that every user and device is continuously authenticated and authorized, regardless of where they connect.
Easy to configure options, add users, and that it has two factor authentication built in. You can configure the system to allow connections on common ports so that you're able to connect from pretty much anywhere in the world.
Configuring and updating my own server is super simple. In my experience, I've always had some difficulty setting up hardware VPN appliances, but OpenVPN was no-nonsense.
The OpenVPN Access Server AMI is a great out of the box VPN solution for your AWS VPC...
OpenVPN offers users a very simple and secure VPN option that is both economical and quick to install. Users are able to easily install it on their client devices.
The availability of client software for all operating systems and mobile devices means my customers can connect regardless of their setup.
Excellent, flexible solution for our Azure environment.